AWS Developer Tools Blog
Category: .NET
Introducing the AWS Message Processing Framework for .NET (Preview)
We are happy to announce the developer preview release of the AWS Message Processing Framework for .NET. This is an AWS-native framework that simplifies the development of .NET message-processing applications that use AWS services such as Amazon Simple Queue Service (Amazon SQS), Amazon Simple Notification Service (Amazon SNS), and Amazon EventBridge. The framework is designed […]
Important changes coming for .NET Framework 3.5 and 4.5 targets of the AWS SDK for .NET
Starting August 15th 2024, the AWS SDK for .NET will end support for .NET Framework 3.5 and will change the minimum .NET Framework version to 4.6.2. Motivation .NET Framework 3.5 was released in 2007 when AWS was in its early stages with just a handful of services. Since then, the complexity of cloud applications and […]
Improved DynamoDB Initialization Patterns for the AWS SDK for .NET
The AWS SDK for .NET includes the Document and Object Persistence programming models, which provide an idiomatic .NET experience for working with Amazon DynamoDB. Beginning in AWSSDK.DynamoDBv2 3.7.203, there are new ways to initialize the document and object persistence models which can improve your application’s performance by reducing thread contention and throttling issues during the first call to DynamoDB. […]
.NET Lambda Annotations Framework is now generally available
We are happy to announce the general availability of the Lambda Annotations Framework for .NET. This new programming model makes the experience of writing Lambda in C# feel more natural for .NET developers by using C# Source Generators. In this post we’ll show how to use framework to simplifying writing .NET Lambda functions that are […]
Introducing the AWS .NET Distributed Cache Provider for DynamoDB (Preview)
We are happy to announce the preview release of the AWS .NET Distributed Cache Provider for DynamoDB. This library enables Amazon DynamoDB to be used as the storage for ASP.NET Core’s distributed cache framework. A cache can improve the performance of an application; an external cache allows the data to be shared across application servers […]
Configuring .NET Garbage Collection for Amazon ECS and AWS Lambda
.NET developers rely on .NET’s automatic memory allocation and garbage collection (GC) mechanisms to handle the memory needs of their applications. For most use cases GC isn’t something developers need to worry about. However, in modern architectures where .NET applications are running in memory constrained environments, like containers and AWS Lambda functions, the GC might […]
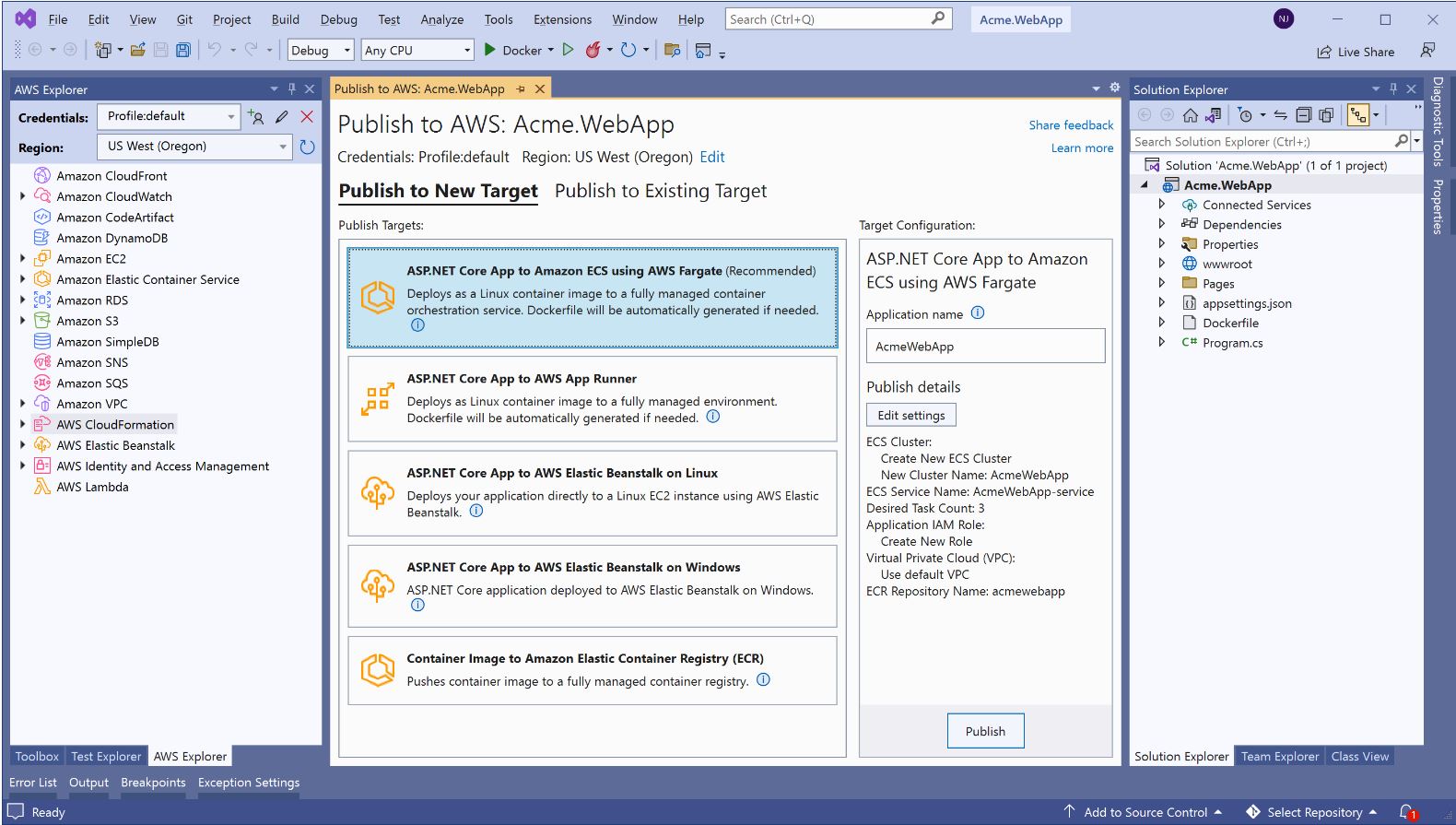
AWS announces a streamlined deployment experience for .NET applications
We are happy to announce the general availability of a new deployment experience in both the Visual Studio and the .NET CLI. This follows the preview announcement from last year. The new deployment experience focuses on the type of application you want to deploy instead of individual AWS services by providing intelligent compute recommendations. You […]
Tips & Tricks: Delaying AWS Service configuration when using .NET Dependency Injection
Tips & Tricks: Delaying AWS Service configuration when using .NET Dependency Injection The AWSSDK.Extensions.NETCore.Setup package provides extensions for enabling AWS Service Client creation to work with native .NET Dependency Injection. Bindings for one or more services can be registered via the included AddAWSService<TService> method and a shared configuration can be added and customized via the […]
Introducing .NET Annotations Lambda Framework (Preview)
Recently we released the .NET 6 managed runtime for Lambda. Along with the new Lambda runtime we have also been working on a new framework for writing .NET 6 Lambda functions called Lambda Annotations. The Annotations framework makes the experience of writing Lambda feel more natural in C#. It also takes care of synchronizing the […]
Build and Deploy a Microsoft .NET Core Web API application to AWS App Runner using CloudFormation
In this blog we show you how to build a Microsoft.NET Web API application with Amazon Aurora Database using AWS App Runner. AWS App Runner makes it easy for developers to quickly deploy containerized web applications and APIs, and helps us start with our source code or a container image. Container workload management tasks, such […]